Leader of DDoS-for-Hire Gang Pleads Guilty to Bomb Threats
A 19-year-old man from the United Kingdom who headed a cybercriminal group whose motto was “Feds Can’t Touch Us” pleaded guilty this week to making bomb threats against thousands of schools.
On Aug. 31, officers with the U.K.’s National Crime Agency (NCA) arrested Hertfordshire resident George Duke-Cohan, who admitted making bomb threats to thousands of schools and a United Airlines flight traveling from the U.K. to San Francisco last month.
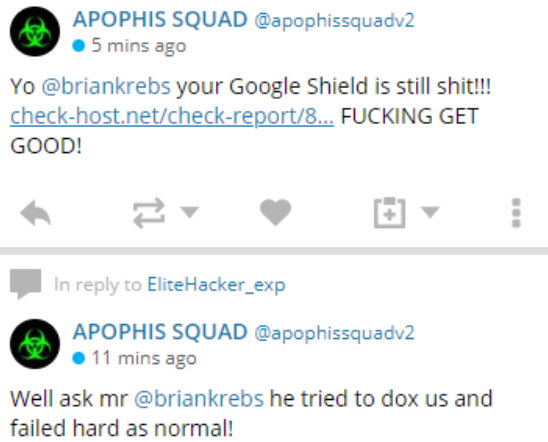
One of many tweets from the attention-starved Apophis Squad, which launched multiple DDoS attacks against KrebsOnsecurity and Protonmail over the past few months.
Duke-Cohan — a.k.a. “7R1D3N7,” “DoubleParallax” and “Optcz1” — was among the most vocal members of a group of Internet hooligans that goes by the name “Apophis Squad,” which for the better part of 2018 has been launching distributed denial-of-service (DDoS) attacks against multiple Web sites, including KrebsOnSecurity and Protonmail.com.
Incredibly, all self-described members of Duke-Cohan’s clique were active users of Protonmail, even as they repeatedly attacked its servers and taunted the company on social media.
“What we found, combined with intelligence provided by renowned cyber security journalist Brian Krebs, allowed us to conclusively identify Duke-Cohan as a member of Apophis Squad in the first week of August, and we promptly informed law enforcement,” Protonmail wrote in a blog post published today. “British police did not move to immediately arrest Duke-Cohan however, and we believe there were good reasons for that. Unfortunately, this meant that through much of August, ProtonMail remained under attack, but due to the efforts of Radware, ProtonMail users saw no impact.”
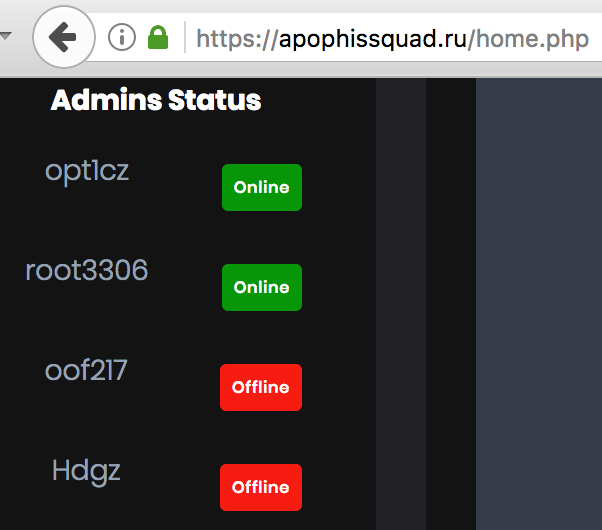
The DDoS-for-hire service run by Apophis Squad listed their members.
On Aug. 9, 2018, the attention-seeking Apophis Squad claimed on their Twitter account that flight UAL 949 had been grounded due to their actions.
“In a recording of one of the phone calls which was made while the plane was in the air, he takes on the persona of a worried father and claims his daughter contacted him from the flight to say it had been hijacked by gunmen, one of whom had a bomb,” the NCA said of Duke-Cohan’s actions in a press release on Sept. 4. “On arrival in San Francisco the plane was the subject of a significant security operation in a quarantined area of the airport. All 295 passengers had to remain on board causing disruption to onward journeys and financial loss to the airline.”
The Apophis Squad modeled itself after the actions of the Lizard Squad, another group of e-fame seeking online hoodlums who also ran a DDoS-for-hire service, called in bomb threats to airlines, DDoSed this Web site repeatedly and whose members were nearly all subsequently arrested and charged with various cybercrimes. Indeed, the Apophis Squad’s Web site and DDoS-for-hire service is hosted on the same Internet server used by a handful of other domains that were tied to the Lizard Squad.
Unsophisticated but otherwise time-wasting and annoying groups like Apophis Squad are a dime a dozen. But as I like to say, each time my site gets attacked by one of them two things usually happen not long after: Those responsible get arrested, and I get at least one decent story out of it. And if Protonmail is right, there are additional charges on the way.
“We believe further charges are pending, along with possible extradition to the US,” the company said. “In recent weeks, we have further identified a number of other individuals engaged in attacks against ProtonMail, and we are working with the appropriate authorities to bring them to justice.”
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.






