‘Blackhole’ Exploit Kit Author Gets 8 Years
A Moscow court this week convicted and sentenced seven hackers for breaking into countless online bank accounts — including “Paunch,” the nickname used by the author of the infamous “Blackhole” exploit kit. Once an extremely popular crimeware-as-a-service offering, Blackhole was for several years responsible for a large percentage of malware infections and stolen banking credentials, and likely contributed to tens of millions of dollars stolen from small to mid-sized businesses over several years.

Fedotov, the convicted creator of the Blackhole Exploit Kit, stands in front of his Porche Cayenne in an undated photo.
According to Russia’s ITAR-TASS news network, Dmitry “Paunch” Fedotov was sentenced on April 12 to seven years in a Russian penal colony. In October 2013, the then 27-year-old Fedotov was arrested along with an entire team of other cybercriminals who worked to sell, develop and profit from Blackhole.
According to Russian security firm Group-IB, Paunch had more than 1,000 customers and was earning $50,000 per month from his illegal activity. The image at right shows Paunch standing in front of his personal car, a Porsche Cayenne.
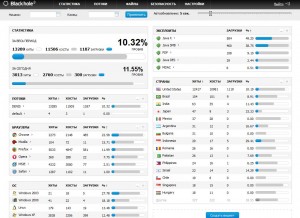
First spotted in 2010, BlackHole is commercial crimeware designed to be stitched into hacked or malicious sites and exploit a variety of Web-browser vulnerabilities for the purposes of installing malware of the customer’s choosing.
The price of renting the kit ran from $500 to $700 each month. For an extra $50 a month, Paunch also rented customers “crypting” services; cryptors are designed to obfuscate malicious software so that it remains undetectable by antivirus software.
Paunch worked with several other cybercriminals to purchase new exploits and security vulnerabilities that could be rolled into Blackhole and help increase the success of the software. He eventually sought to buy the exploits from other cybercrooks directly to fund a pricier ($10,000/month) and more exclusive exploit pack called “Cool Exploit Kit.”
As documented on this blog in January 2013 (see Crimeware Author Funds Exploit Buying Spree), Paunch contracted with a third-party exploit broker who announced that he had a $100,000 budget for buying new, previously undocumented “zero-day” vulnerabilities.
Not long after that story, the individual with whom Paunch worked to purchase those exclusive exploits — a miscreant who uses the nickname “J.P. Morgan” — posted a message to the Darkode[dot]com crime forum, stating that he was doubling his exploit-buying budget to $200,000.
In October 2013, shortly after news of Paunch’s arrest leaked to the media, J.P. Morgan posted to Darkode again, this time more than doubling his previous budget — to $450,000.
“Dear ladies and gentlemen! In light of recent events, we look to build a new exploit kit framework. We have budgeted $450,000 to buy vulnerabilities of a browser and its plugins, which will be used only by us afterwards! ”
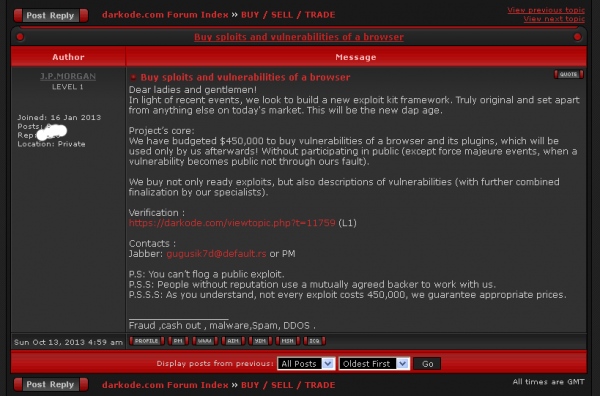
J.P. Morgan alludes to his former partner’s arrest, and ups his monthly exploit buying budget to $450,000.
The Russian Interior Ministry (MVD) estimates that Paunch and his gang earned more than 70 million rubles, or roughly USD $2.3 million. But this estimate is misleading because Blackhole was used as a means to perpetrate a vast array of cybercrimes. I would argue that Blackhole was perhaps the most important driving force behind an explosion of cyber fraud over the past three years. A majority of Paunch’s customers were using the kit to grow botnets powered by Zeus and Citadel, banking Trojans that are typically used in cyberheists targeting consumers and small businesses.
For more about Paunch, check out Who is Paunch?, a profile I ran in 2013 shortly after Fedotov’s arrest that examines some of the clues that connected his online criminal persona with his personal social networking profiles.
Tags: BlackHole Exploit Kit, Cool Exploit Kit, Dmitry Fedotov, Group-IB, J.P. Morgan, Paunch, Russian Interior Ministry
This entry was posted on Thursday, April 14th, 2016 at 10:34 am and is filed under A Little Sunshine, Ne'er-Do-Well News. You can follow any comments to this entry through the RSS 2.0 feed. You can skip to the end and leave a comment. Pinging is currently not allowed.
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.