Banks: Credit Card Breach at CiCi’s Pizza
Wal-Mart says tech investments will boost online sales
June 3, 2016SoftBank adds to Alibaba sale, bringing total to $10 billion
June 3, 2016CiCi’s Pizza, an American fast food business based in Coppell, Texas with more than 500 stores in 35 states, appears to be the latest restaurant chain to struggle with a credit card breach. The data available so far suggests that hackers obtained access to card data at affected restaurants by posing as technical support specialists for the company’s point-of-sale provider, and that multiple other retailers have been targeted by this same cybercrime gang.
 Over the past two months, KrebsOnSecurity has received inquiries from fraud fighters at more than a half-dozen financial institutions in the United States — all asking if I had any information about a possible credit card breach at CiCi’s. Every one of these banking industry sources said the same thing: They’d detected a pattern of fraud on cards that all had one thing in common: They’d all been used in the last few months at various CiCi’s Pizza locations.
Over the past two months, KrebsOnSecurity has received inquiries from fraud fighters at more than a half-dozen financial institutions in the United States — all asking if I had any information about a possible credit card breach at CiCi’s. Every one of these banking industry sources said the same thing: They’d detected a pattern of fraud on cards that all had one thing in common: They’d all been used in the last few months at various CiCi’s Pizza locations.
Earlier today, I finally got around to reaching out to the CiCi’s headquarters in Texas and was referred to a third-party restaurant management firm called Champion Management. When I called Champion and told them why I was inquiring, they said “the issue” was being handled by an outside public relations firm called SPM Communications.
I never did get a substantive response from SPM, which according to their email and phone messages closes at 1 pm on Fridays during the summer. So I decided to follow up on a tip I’d received from a fraud fighter at one affected bank who said they’d heard from the U.S. Secret Service that the fraud was related to a breach or security weakness at Datapoint (CiCi’s point-of-sale provider).
Incredibly, I went to look up the contact information for datapoint[dot]com, and found that Google was trying to prevent me from visiting this site: According to the search engine giant, Datapoint’s Web site appears to be compromised and trying to foist malicious software on visitors! Unless you know what you’re doing, please resist the temptation to visit this site.
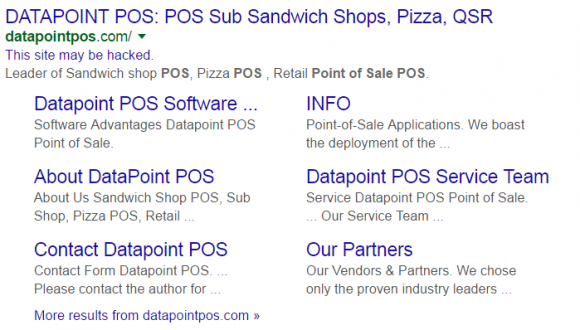
Google thinks Datapoint’s Web site is trying to foist malicious software.
A quick look at Datapoint’s site via a virtual machine-protected Linux browser indicates that CiCi’s Pizza is indeed one of the company’s largest clients. The Secret Service did not immediately respond to requests for comment.
Undeterred, I phoned and emailed Datapoint, and heard back via email from Stephen P. Warne, vice president of service and support for the company. Warne said I was jumping to conclusions and that my “sources” must have had a beef with the company. Here’s his email to me, verbatim:
If you did indeed talk to the Secret Service you would know that the breaches they have investigated involved multiple POS vendors in one particular franchise, including Harbortouch and Granbury Restaurant Systems.
You would also know that not one Agent we spoke and cooperated with came to any conclusion of wrong doing on our part after scans months ago. The SS actually helped point out that these hackers used among Team Viewer, Screen Connect and some others they installed.
All of these attacks have been traced to social engineering/Team Viewer breaches because stores from SEVERAL POS vendors let supposed techs in to conduct ‘support’. Nothing to do with any of our support mechanisms which are highly restricted and well within PCI Compliance.
I won’t say much else on this as this is not a Datapoint breach. We just happened to have by far the most systems in that particular franchise overwhelmingly.
Interestingly, this apparent breach comes to light amid a great deal of speculation on Reddit and other places online about a possible data breach at Teamviewer. The idea that countless credit card terminals or cash registers at CiCi’s Pizza establishments and other businesses could have been compromised by cybercriminals who simply phoned up the establishments posing as tech support technicians for various point-of-sale vendors is remarkable (and frankly pretty ingenious).
I’ll no doubt have updates to this story as the weekend progresses. Stay tuned.
Tags: Champion Management, CiCi’s Pizza breach, Datapoint, SPM Communications, Stephen P. Warne, U.S. Secret Service
This entry was posted on Friday, June 3rd, 2016 at 7:47 pm and is filed under Data Breaches. You can follow any comments to this entry through the RSS 2.0 feed. You can skip to the end and leave a comment. Pinging is currently not allowed.

